Technology moves fast—and if you’re trying to keep up with the latest buzz around digital trends, emerging devices, and modern software architecture, it can feel overwhelming. You’re not just looking for headlines; you want clear explanations, practical insights, and real-world applications that actually make sense.
This article is built to cut through the noise. We’ll break down what’s trending in the tech industry, explore the tools and devices shaping the next wave of innovation, and highlight practical tech hacks you can apply immediately. Whether you’re curious about evolving software frameworks or how scalable shaxs systems are influencing digital infrastructure, you’ll find focused, actionable insights here.
Our analysis is grounded in continuous monitoring of industry developments, product releases, and architectural best practices. We prioritize clarity over hype—so you can understand not just what’s happening in tech, but why it matters and how to use it to your advantage.
The modern communication trilemma pits security, scalability, and uptime against each other. Strengthen encryption and latency spikes. Add users and systems crash. Chase 99.999% availability and vulnerabilities creep in. Legacy monoliths force these trade-offs.
Here’s a practical blueprint:
- Break platforms into microservices so failures stay isolated.
- Adopt zero-trust access, verifying every request.
- Use container orchestration to auto-scale during traffic surges.
- Implement real-time monitoring with automated failover.
For example, scalable shaxs systems combine horizontal scaling with encrypted service meshes, proving you don’t have to sacrifice protection for growth. Start with one service, refactor incrementally, measure load, then expand. No compromises required.
Laying the Bedrock: Non-Negotiable Security Protocols
Zero-Trust Architecture
Start with an anecdote about the day an “internal-only” dashboard exposed staging credentials to the whole company. I remember the sinking feeling (the kind you get when you hit “reply all” by accident). That’s when zero-trust architecture clicked. Zero trust means never trust, always verify—even inside your own network. Every service call must prove its identity using mutual TLS (mTLS), where both client and server authenticate each other with certificates. Add strict least-privilege access controls (users and services get only what they need, nothing more). Some argue this slows teams down. In practice, automation and policy-as-code make it scalable—especially in scalable shaxs systems.
End-to-End Encryption (E2EE)
E2EE ensures only the communicating users can read messages—keys live on their devices, not on servers (even admins can’t peek). TLS protects data in transit, but E2EE protects it from everyone in between. The challenge? Key management and recovery. Lose the keys, lose the data (no dramatic “hacking montage” rescue scene).
Immutable Audit Logs
An immutable log is tamper-proof recordkeeping—often append-only and cryptographically signed. It’s vital for forensics and debugging. Some say it’s overkill—until the day you need proof of what really happened.
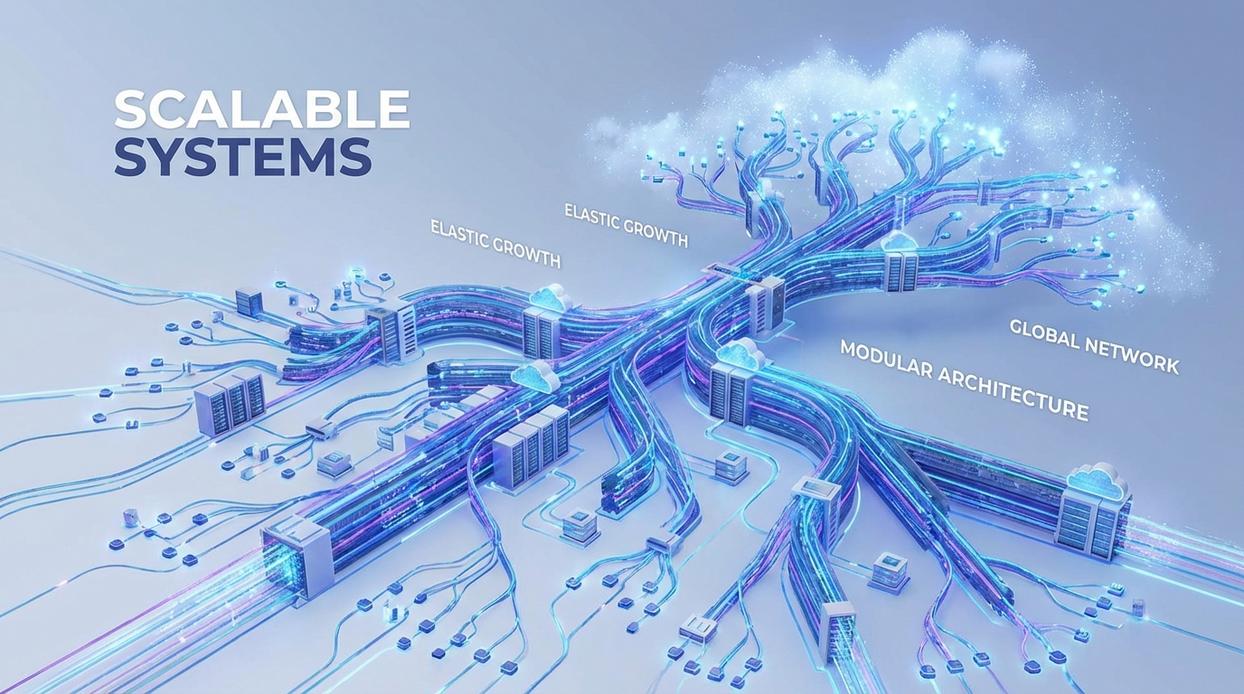
From One to a Million: Architecting for Elastic Scalability
Scaling from a handful of users to millions isn’t luck. It’s architecture. And this is where monoliths start to crack.
Microservices vs. Monoliths
A monolith is a single, tightly coupled application where all components deploy together. Change one line in authentication? Redeploy the entire system. That’s manageable at 1,000 users. At 1,000,000, it’s friction.
Microservices split functionality into independent services—authentication, message delivery, notifications, billing—each deployable and scalable on its own. If login traffic spikes during a product launch, you scale only the auth service. If messages surge, scale delivery nodes. You don’t overpay for idle resources.
Critics argue monoliths are simpler (and they are—at first). Fewer moving parts, easier debugging. But simplicity that blocks INDEPENDENT SCALING becomes a liability. True elasticity demands separation of concerns.
For a deeper architectural breakdown, see comparing shaxs architecture to microservices models.
Message Queues and Event Streaming
Here’s what many competitors miss: scaling isn’t just about compute—it’s about FLOW CONTROL.
Tools like RabbitMQ and Kafka act as intermediaries between services. A message queue stores tasks until consumers process them. An event stream records ordered events for distributed systems.
If 500,000 users send messages at once (think viral moment, not average Tuesday), queues absorb the surge. Producers don’t crash consumers. Kafka even guarantees durability and replayability—critical for reliability and compliance.
This decoupling is foundational to scalable shaxs systems.
Stateless Application Tiers
A stateless service stores no session data locally. Every request contains everything needed.
Why it matters: any server can handle any request. That enables horizontal scaling and simple load balancing. Add instances. Remove instances. No drama.
STATELESSNESS is what turns infrastructure into elastic clay instead of rigid stone.
Designing for Zero Downtime: Advanced Reliability Patterns
Zero downtime sounds like a fantasy—until your checkout page crashes during peak traffic (cue the horror movie music). The difference between resilient and fragile systems often comes down to architecture choices.
Redundancy and Failover: Active-Active vs Active-Passive
Active-Active means multiple nodes run simultaneously, sharing traffic. If one fails, others continue seamlessly. Active-Passive keeps a standby node idle until failure occurs.
- Active-Active: Higher availability, better load distribution, higher cost.
- Active-Passive: Cost-efficient, simpler setup, slightly slower failover.
Critics argue active-active is overkill for smaller workloads. Fair. But automated failover—powered by health checks and load balancers—reduces human intervention and recovery time dramatically (Google’s SRE research shows automation cuts incident resolution time significantly).
Pro tip: Always test failover in staging. Chaos engineering exists for a reason.
Database Replication and Distribution
A primary-replica setup routes writes to a primary database and distributes reads to replicas. This improves read scalability and enables failover. However, replication lag can introduce stale reads.
Geo-replication distributes data across regions. Compared to single-region replication, geo-distribution improves disaster recovery but increases complexity and latency.
Think Netflix-style resilience versus a single data center gamble.
The Circuit Breaker Pattern
A circuit breaker stops requests to a failing service once error thresholds are exceeded. Instead of cascading failure, it “opens” the circuit and allows recovery time.
Without it: one failing API drags everything down.
With it: the system degrades gracefully.
For scalable shaxs systems, combining redundancy, replication, and circuit breakers creates layered defense—because reliability isn’t one feature. It’s a strategy.
The Unified Framework: Where Security and Performance Converge
A scalable architecture isn’t just about speed—it’s defense by design. Auto-scaling groups automatically add instances during traffic spikes, while load balancers distribute requests so no single server becomes a bottleneck. In a DDoS attack (when attackers flood your system with traffic), this elasticity absorbs and disperses malicious surges.
Try this:
- Configure auto-scaling thresholds based on CPU and request rates.
- Place a load balancer in front of every public-facing service.
Service meshes like Istio or Linkerd add another layer. They enforce mTLS (mutual Transport Layer Security, meaning services verify each other), manage retries/timeouts, and provide observability—without code changes (yes, really).
Finally, treat monitoring as security:
- Set anomaly alerts on traffic patterns.
- Track latency deviations.
Reliable telemetry in scalable shaxs systems often flags breaches before humans notice.
Years ago, I rebuilt a failing chat app that crashed every launch day (not fun). The fix wasn’t a bigger server—it was a blueprint: decoupled microservices, a zero-trust security model (zero-trust means verifying every request), plus message queues and redundancy for resilience. In practice, security, scalability, and reliability rise together. So, assess your stack today and refactor the one weak link blocking scalable shaxs systems. Start small, but start with architectural intent from day one.
Turn Insight Into Action with Shaxs
You came here to cut through the noise and understand what’s really happening in today’s fast-moving tech landscape. Now you have the clarity to navigate emerging devices, evolving software architecture, and the digital trends shaping tomorrow’s innovations.
The real challenge isn’t access to information—it’s knowing how to apply it before the next wave hits. Falling behind on tech shifts can mean wasted resources, outdated systems, and missed competitive advantages. Staying proactive is no longer optional.
That’s where scalable shaxs systems make the difference. By combining sharp industry insight with practical, real-world tech strategies, you’re equipped to build smarter workflows, future-proof your infrastructure, and move with confidence.
If you’re ready to stop reacting to trends and start leveraging them, now’s the time. Explore the latest insights, implement the proven tech hacks, and align your strategy with forward-thinking solutions trusted by a growing community of tech-driven professionals.
Don’t let rapid innovation outpace you—dive deeper, apply what you’ve learned, and take control of your next tech move today.
