If you’re searching for clarity on shaxs vs microservices, you’re likely trying to decide which architectural approach makes the most sense for your next build—or whether the comparison even makes sense in the first place. With constant buzz around modular systems, distributed design, and scalable software patterns, it’s easy to get lost in opinions that lack real technical depth.
This article cuts through that noise. We break down the architectural principles behind both concepts, examine how they impact scalability, maintainability, and deployment workflows, and highlight where each approach fits in modern software ecosystems. Whether you’re designing a new platform or rethinking an existing stack, you’ll find practical insights grounded in real-world implementation patterns and current industry practices.
Our analysis draws on up-to-date software architecture research, active developer discussions, and hands-on evaluation of emerging tech frameworks—so you can make decisions based on substance, not hype.
SHA-1 vs. Microservices: Clearing the Confusion
You’ve seen the terms SHA-1 and microservices and wondered how they compare. Here’s the catch: they operate in entirely different domains. SHA-1 (Secure Hash Algorithm 1) is a cryptographic hash function—a mathematical process that turns data into a fixed-length string for integrity checks. Microservices, by contrast, are an architectural style where applications are built as small, independent services.
Comparing shaxs vs microservices is like comparing a brick to a city blueprint.
So what should you do?
- Use modern hashes like SHA-256, not SHA-1.
- Choose microservices only when scalability and team autonomy truly demand it.
Deep Dive: What is SHA-1?
SHA-1 (Secure Hash Algorithm 1) is a cryptographic hash function—a mathematical algorithm that converts any input into a fixed 160-bit string known as a hash. In practice, that means whether you feed it a short password or a full-length movie file, it outputs a 40-character hexadecimal value. Think of it as a digital fingerprint for data: even a one-letter change produces a completely different print.
Its primary purpose is data integrity, meaning confirmation that information hasn’t been altered in transit or storage. For example, if you download software, the publisher can provide a SHA-1 hash; if your computed hash matches, the file is intact.
However, SHA-1 is now deprecated. In 2017, Google and CWI Amsterdam demonstrated the first practical “collision attack,” generating two different files with the same SHA-1 hash, proving the algorithm’s weaknesses (SHAttered project). NIST had already recommended moving away from SHA-1 years earlier. Consequently, modern systems use stronger successors like SHA-256.
Historically, SHA-1 powered digital signatures, SSL certificates, and Git’s integrity checks. Yet just as debates like shaxs vs microservices evolve with evidence, cryptography advances when proof exposes flaws. Pro tip: always verify which hash standard your tools rely on. Stay updated.
Understanding the Big Picture: What Are Microservices?
Microservices are a software architecture style that structures a large application as a collection of small, independently deployable services. Each service focuses on a specific business function and communicates with others through lightweight APIs (Application Programming Interfaces, which let software systems “talk” to each other).
Think of it like this: instead of constructing one giant skyscraper (a monolithic app), you build a campus of smaller, specialized buildings that work together. If the cafeteria closes, the library and offices still function. That’s resilience in action.
Core Features and Benefits
- Independent Deployment: Teams can update one service without redeploying the entire application.
- Improved Scalability: Scale only what you need. If user logins spike, scale the authentication service—not the whole system.
- Resilience: If one service fails, others continue running (like Netflix streaming even if recommendations glitch).
- Technology Flexibility: Different services can use different tech stacks based on performance needs.
- Easier Maintenance: Smaller codebases are faster to debug and enhance.
Companies like Netflix, Amazon, and Uber rely on microservices to scale millions of users globally (IBM, 2023).
Some argue monoliths are simpler to manage—and for small apps, that’s often true. But at scale, microservices offer agility monoliths struggle to match.
For deeper protection strategies, review security best practices in shaxs based applications.
When debating shaxs vs microservices, the real question is flexibility versus simplicity.
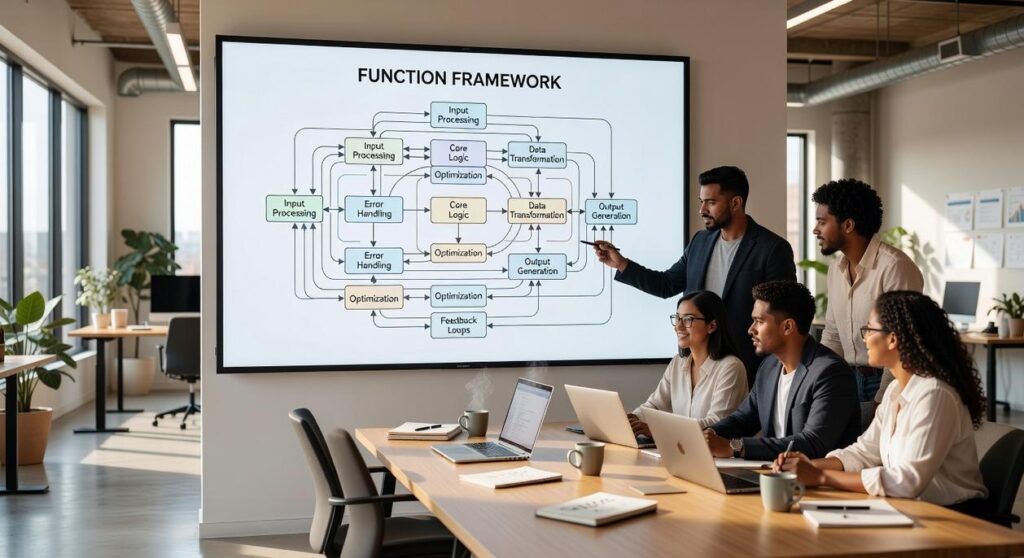
The Core Comparison: Function vs. Framework

At first glance, comparing SHA-1 and microservices can feel like comparing apples to engine parts. They both live in the tech world—but they solve entirely different problems. So let’s clarify.
SHA-1 (Secure Hash Algorithm 1) is a cryptographic algorithm, meaning it’s a mathematical function designed to transform data into a fixed-length string called a hash (a unique digital fingerprint). Its primary job is verifying data integrity—making sure information hasn’t been altered. For example, when you download a file, a SHA-1 hash can confirm it hasn’t been tampered with during transfer (though modern systems now prefer stronger alternatives like SHA-256 due to collision vulnerabilities, per NIST guidance).
Microservices, on the other hand, are an architectural pattern—a blueprint for designing software systems. Instead of building one massive application (a monolith), developers split systems into small, independent services that communicate over APIs. Think Netflix: separate services handle recommendations, billing, and streaming (Martin Fowler, 2014).
Here’s the difference clearly laid out:
| Category | SHA-1 | Microservices |
|————–|————|——————-|
| Purpose | Verify data integrity | Structure applications |
| Type | Cryptographic Algorithm | Architectural Pattern |
| Scope | Applied to data | Applied to system design |
| Key Benefit | Security | Scalability & Flexibility |
In simpler terms, SHA-1 is a specific type of lock for a door. Microservices is the architectural plan for the entire house, deciding where doors and rooms go.
Some might argue that both influence “security.” True—but at vastly different levels. One protects data. The other organizes systems. That’s the real distinction behind shaxs vs microservices.
The Unlikely Connection: Where Hashing Meets Architecture
At first glance, hashing algorithms and microservices seem unrelated (like comparing blueprints to padlocks). But in modern systems, they intersect CONSTANTLY.
In a microservices-based application, hashing protects communication and data at multiple layers. For API Security, services often sign requests using cryptographic hashes to verify authenticity and prevent tampering. This ensures that when Service A calls Service B, the payload hasn’t been altered in transit—a direct benefit for trust and system reliability.
For Data Storage, a dedicated user service stores passwords as hashed values using secure algorithms like Argon2 or bcrypt. These algorithms are intentionally slow and salted (randomized data added before hashing), reducing the risk of brute-force attacks.
For Inter-service Integrity, one service can send a file alongside its SHA-256 hash. The receiving service recalculates the hash to confirm the file arrived intact.
In debates like shaxs vs microservices, hashing quietly powers the security backbone behind scalable design.
Applying This Knowledge to Your Tech Strategy
Your original confusion in shaxs vs microservices comes down to category error. A hash function like SHA-1 is a cryptographic tool (now considered insecure per NIST), whereas microservices is an architectural pattern for structuring applications.
When you mix those up, you risk flawed planning.
So, what should you do next?
- Audit security: replace SHA-1 with SHA-256 or bcrypt for passwords.
- Evaluate scale: map features into independent services and test deployment complexity.
- Document decisions: tie each tool to its purpose.
In practice, clear distinctions lead to safer, scalable systems long term.
Choosing Between shaxs vs microservices for Your Next Build
You set out to understand the real differences between shaxs vs microservices, and now you have a clear picture of how each approach impacts scalability, deployment speed, system complexity, and long‑term maintenance. Instead of guessing which architecture fits your product, you can now evaluate them based on your growth plans, team structure, and technical goals.
The biggest pain point isn’t just choosing the wrong architecture — it’s wasting time and resources rebuilding later because the foundation couldn’t scale. Whether you’re battling deployment bottlenecks, service sprawl, or performance limitations, the right decision today prevents expensive rewrites tomorrow.
Now it’s time to act. Audit your current system requirements, map out your projected scale, and identify where complexity is helping — or hurting — your progress. If you want proven, no‑fluff breakdowns that simplify tough tech decisions and keep you ahead of fast‑moving digital trends, explore more expert insights on Shaxs — trusted by tech professionals who want clarity, not confusion. Start optimizing your architecture strategy today.