I’ve seen too many dev teams treat compliance like a last-minute checkbox before launch.
You’re probably here because you need to meet SOC 2, GDPR, or HIPAA requirements without grinding your development process to a halt. The current approach isn’t working.
Here’s the reality: when you treat security as something you add at the end, you’re setting yourself up for failed audits and expensive rewrites.
I spent years building systems where compliance was an afterthought. It was painful every single time. Then I learned to flip the model.
This article shows you how to build security into your development lifecycle from day one. Not as a burden. As a design principle.
The framework I’m sharing comes from real implementation experience. I’ve worked through the compliance process enough times to know what actually works and what’s just security theater.
You’ll learn how to improve software architecture so compliance becomes a natural outcome instead of a bottleneck. We’re talking about practical steps you can start using today.
No theory. No corporate security jargon. Just the process that turns compliance from a nightmare into something your team handles without breaking stride.
meetshaxs breaks down complex tech processes into steps you can actually use. That’s what we’re doing here.
Decoding the Compliance Maze: More Than a Checklist
You’ve probably heard the acronyms thrown around.
GDPR. PCI DSS. HIPAA. SOC 2.
They all sound like alphabet soup until you’re the one who has to deal with them. And then they become very real very fast.
Here’s what each one actually does. GDPR protects user data privacy (mostly in Europe but it affects US companies too). PCI DSS covers payment card information. HIPAA handles health records. SOC 2 proves your service organization can be trusted with customer data.
Different frameworks. Same basic idea.
Some people treat compliance like it’s just paperwork. Check the boxes, pass the audit, move on. They think if they can scramble together evidence once a year, they’re good.
That’s the OLD way.
And honestly? It’s exhausting. I’ve watched teams pull all-nighters before audits, frantically gathering screenshots and documents they should’ve collected months ago. It’s stressful and it doesn’t actually make you MORE secure.
Here’s the comparison that matters.
Audit-driven compliance: You spend 11 months ignoring your controls. Then you spend one month in panic mode trying to prove everything works. You pass (maybe). Then you forget about it until next year.
Continuous compliance: You monitor your security controls year-round. You gather evidence as you go. When audit time comes, you’re ready because you’ve BEEN ready.
Which one sounds better?
The second approach isn’t just easier. It’s what regulators actually want to see. They don’t care if you can fake it for a week. They want proof your controls work consistently. In the evolving landscape of gaming regulations, developers must adopt a consistent approach that not only satisfies compliance but also builds genuine trust among players, as highlighted in the recent discussions surrounding platforms like Meetshaxs. In the face of stringent gaming regulations, developers like Meetshaxs are leading the charge by implementing robust, consistent controls that not only meet compliance but also enhance player trust and safety.
Think about improve software meetshaxs in future planning. You wouldn’t wait until launch day to test your code, right?
Same logic applies here.
Your compliance process should show maturity. Repeatable steps. Real risk management. Not just a checklist you dust off once a year.
The ‘Shift Left’ Revolution: Integrating Security from Day One
You’ve probably heard developers complain about security teams blocking their releases at the last minute.
It happens all the time. A team spends weeks building a feature, only to have security find a problem right before launch. Everything stops. Deadlines slip. People get frustrated.
Here’s what most teams don’t realize.
The Real Cost of Waiting
Finding a security flaw during the design phase? That might cost you an hour of rework. Maybe two.
Find that same flaw in production? You’re looking at thousands of dollars. Emergency patches. Customer notifications. Possible data breaches. The difference isn’t small. It’s massive.
I’ve seen teams at meetshaxs track these costs. The numbers don’t lie.
This is where shifting left comes in.
The idea is simple. Move security earlier in your Software Development Lifecycle. Don’t wait until deployment to think about vulnerabilities. Start during design and coding.
Some people argue this slows down development. They say security should stay separate so developers can move fast without interference.
But that’s backwards thinking.
When you improve software meetshaxs by building security in from the start, you actually move faster. You catch problems when they’re cheap to fix. You don’t get surprised at launch. I put these concepts into practice in Software Meetshaxs Update.
What DevSecOps Actually Means
Forget the buzzword for a second.
DevSecOps is just the practical side of shifting left. You make security everyone’s job, not just the security team’s problem. You automate security checks right into your CI/CD pipeline.
A developer commits code. Automated tests run. Security scans happen. Problems get flagged before they reach production.
No gatekeepers. No last-minute surprises.
Security becomes a partner that helps you ship safely instead of a blocker that says no. Your team can move fast because you’ve built the guardrails into the process itself. By embracing the Advantages of Meetshaxs Software, gaming developers can enhance their workflow, allowing security to seamlessly integrate into the development process and empowering teams to innovate without unnecessary delays. By leveraging the Advantages of Meetshaxs Software, gaming developers can seamlessly integrate security into their workflows, ensuring that the development process remains agile and efficient without compromising safety.
That’s the shift left revolution. Earlier detection. Lower costs. Faster shipping.
A Practical Framework: 4 Pillars of Automated Security for Compliance
Let me clear something up right away.
When people talk about automated security for compliance, they usually make it sound more complicated than it needs to be.
You’ve probably heard terms like “continuous monitoring” or “policy enforcement” thrown around. But what do those actually mean for your systems?
Here’s the truth. Compliance isn’t about checking boxes once a year. It’s about building systems that stay secure without you babysitting them every single day.
That’s where automation comes in.
But before we get into the framework, let me explain what I mean by automated security. It’s not some magic solution that fixes everything while you sleep (though that would be nice). It’s a set of processes that run on their own, catching problems before they become violations.
Think of it this way. Manual compliance is like checking your door locks every hour. Automated compliance is installing a system that alerts you the second something’s wrong.
Now, most frameworks you’ll find online are either too vague to use or so technical that you need a PhD to understand them. I wanted something different. Something you could actually implement.
So I broke it down into four pillars.
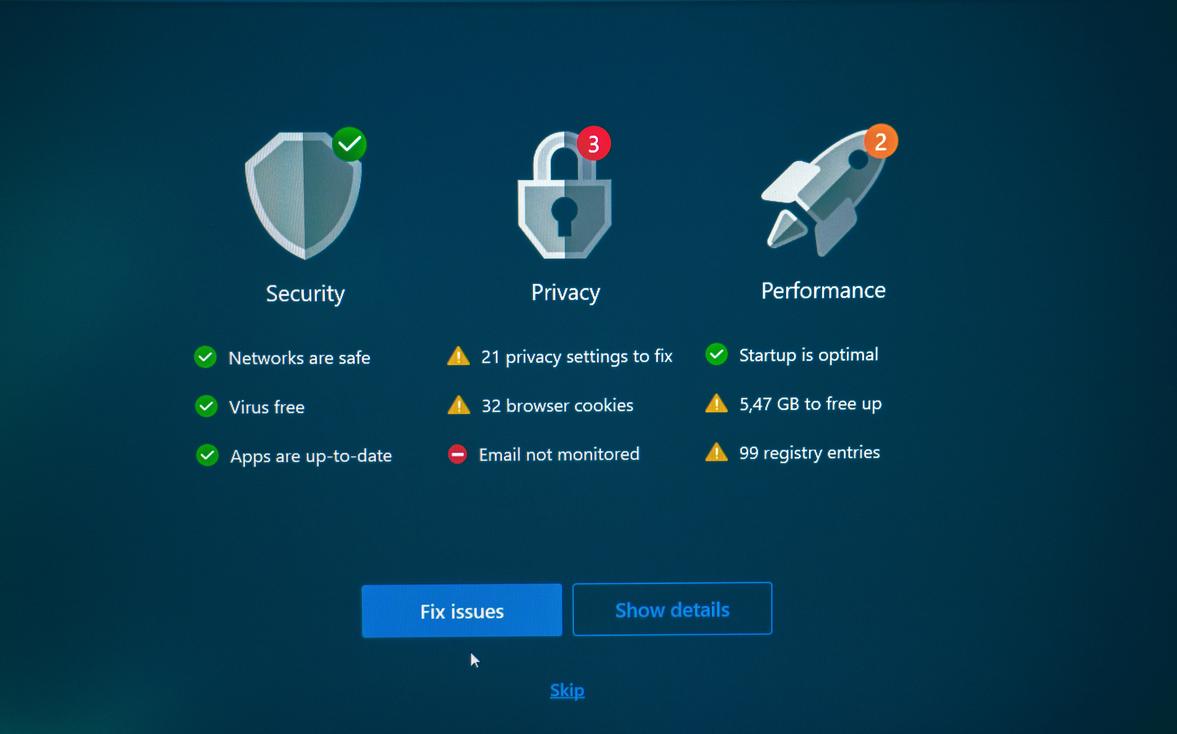
Pillar 1: Continuous Monitoring
This means watching your systems all the time. Not just during audits. You need tools that track who accesses what, when they do it, and whether it follows your policies.
Pillar 2: Automated Policy Enforcement
Your security rules should apply themselves. When someone tries to access data they shouldn’t, the system blocks them. No waiting for approval. No manual intervention.
Pillar 3: Real-Time Reporting
Compliance officers need data fast. Automated reporting gives you up-to-date information without digging through logs for hours. You can see the advantages of meetshaxs software when it comes to streamlining this exact process.
Pillar 4: Incident Response Automation This is something I break down further in Trend of Meetshaxs Software.
When something goes wrong, speed matters. Automated responses can isolate threats, alert your team, and start remediation before damage spreads.
Here’s what makes this framework work. Each pillar supports the others. Monitoring feeds your reporting. Policy enforcement prevents incidents. And when incidents do happen, your response system kicks in automatically.
You don’t need to improve software meetshaxs from scratch to get started. Most organizations already have pieces of this in place. The goal is connecting them so they work together. By leveraging existing tools and systems, organizations can seamlessly connect their resources to enhance collaboration and ultimately Improve Software Meetshaxs in Future. To truly harness the potential of your organization’s capabilities, it’s essential to focus on strategies that will Improve Software Meetshaxs in Future, ensuring that all existing systems are effectively integrated for optimal collaboration.
I’ve seen companies spend months trying to automate everything at once. That’s a mistake. Start with one pillar. Get it running smoothly. Then move to the next.
The point isn’t perfection. It’s progress that actually sticks.
Build Secure, Stay Compliant
You came here looking for a way to balance speed with security.
Now you have it. A four-pillar framework that lets you ship fast without cutting corners on compliance.
The old way treated security as a checkpoint at the end. That creates friction and slows everything down. This approach bakes it into your development process from the start.
When you shift security left and automate it, compliance becomes part of your engineering culture. Not a separate burden that drags on your team.
Here’s what works: DevSecOps turns security into a natural outcome of building quality software. You’re not choosing between moving fast and staying secure anymore.
Start small and build from there. Pick one pillar and run with it. Maybe you implement an SCA tool to scan your open-source dependencies. Get that working and then move to the next piece.
The framework is simple but it works. Security doesn’t have to slow you down if you build it in from the beginning.
Your next step is clear. Choose your starting point and take action. improve software meetshaxs gives you the roadmap. Now it’s time to use it.

